
Life as a CISO in 2026: the hidden sixth day
What life as a CISO looks like in 2026: overtime, AI governance, board pressure and burnout – plus why most cybersecurity leaders would still choose the job all over again.
Read More
Supply chain security has, conventionally, been framed around the idea that you have to identify the weakest link to reduce risk. But modern digital infrastructure doesn’t behave like a chain – it behaves more like a network.
And in a network, the most dangerous point is not necessarily the weakest node – it’s often the most connected one.
Research from the 2026 Black Kite Third-Party Breach Report shows how cyber incidents increasingly propagate through supplier ecosystems rather than remaining isolated within a single organisation. Widely shared technology providers can create systemic exposure when they’re compromised, affecting multiple downstream customers.
Which means supply chain risk is becoming ecosystem risk. A breach affecting a critical provider could ripple across many organisations that rely on that supplier – amplifying the impact far beyond the original victim.
If you lead security at an organisation that works with external vendors, this means it’s time to rethink how you approach third-party security.
Most organisations now rely on a relatively small number of shared platforms – cloud providers, SaaS services, software libraries and technology partners embedded throughout their operations.
That concentration creates efficiency and speed, but it also creates fragility. Because when widely used providers experience security failures, the consequences can spread across multiple organisations that share the same dependency (like the Cloudflare outage last year).
The Black Kite research highlights this challenge as a problem of dependency concentration. The risk used to depend primarily on whether a supplier had strong security controls, but now it’s also very much about how many organisations rely on that supplier, and how deeply it’s integrated into their systems.
This is why modern third-party risk management has to gradually shift from vendor checklists to ecosystem visibility – understanding where dependencies cluster and where the largest potential blast radius might be.
At first glance, organisations do appear to be making progress on software supply chain transparency. The 2026 report from Manifest, Beyond the Black Box, finds that 60% of organisations now generate Software Bills of Materials (SBOMs) to catalogue the components inside their software.
But the report draws a crucial distinction between generating transparency artefacts and using them effectively.
Overall SBOM usage stands at 41.8%, which Manifest defines as organisations that either generate SBOMs or actively manage and consume them as part of their security processes.
Many organisations are still struggling to operationalise supply chain data.
The report finds that:
More than just a lack of information, the challenge here is turning visibility into actionable risk management. Security teams may receive SBOMs, provenance records or other transparency artefacts from vendors during procurement. But without processes to ingest and continuously monitor that information, those artefacts provide limited operational value.
AI is now introducing additional layers of dependency across the technology stack. Manifest’s research shows 63% of organisations report shadow AI usage, where tools, models or integrations are adopted without clear oversight from security or procurement teams.
At the same time, 56.7% of organisations say they are training open-weight AI models on internal data, which introduces new risks around data exposure, licensing and governance. And 93% say their organisations still have significant room for improvement in understanding the legal, licensing and IP obligations surrounding AI.
The Manifest report concludes that AI systems are reintroducing familiar supply chain problems – opaque dependencies, uncertain provenance and unclear accountability across models, datasets and third-party services.
For security leaders, the key question in third-party risk is, increasingly, how many organisations depend on each vendor – and what happens if that vendor fails.
Answering that question requires a broader view of digital supply chains – the ability to map shared dependencies and understand where ecosystem concentration exists, then ensure transparency across suppliers.
Because in today’s connected technology landscape, the most dangerous supplier may just be the one everyone relies on.
Join the newsletter to receive the latest updates in your inbox.

What life as a CISO looks like in 2026: overtime, AI governance, board pressure and burnout – plus why most cybersecurity leaders would still choose the job all over again.
Read More
AI hype is peaking. Dr Rumman Chowdhury explains why use cases remain limited, AGI definitions are shifting, and investors are starting to question the narrative.
Read More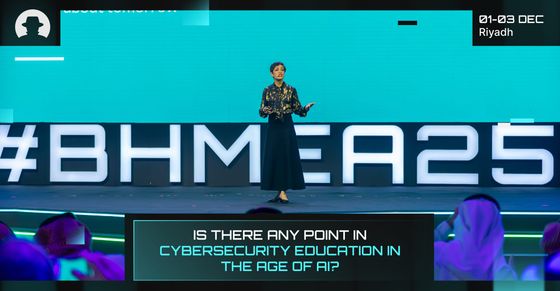
Is cybersecurity education still relevant in the age of AI? Dr Rumman Chowdhury explores how AI is reshaping learning, expertise, and the skills security professionals need.
Read More